The root user in Linux is the system’s superuser — an account with unrestricted access to every file, process, and system function on the computer. Root can read and modify any file regardless of permissions, install and remove any software, manage all user accounts, and change any system setting. Because of this unlimited power, root should never be used for everyday tasks. Instead, Linux provides sudo to grant temporary, targeted root privileges for specific administrative commands only.
Introduction: The Most Powerful Account on Your System
Every Linux system has an account that stands apart from all others. It cannot be locked out. It bypasses nearly every security restriction. It can read anyone’s private files, modify the operating system itself, delete critical system components, and do anything else imaginable to the computer. This account is root — and understanding it thoroughly is one of the most important things a Linux user can do.
The root account is not a mistake or a legacy relic. It exists because someone needs to be able to do everything — to install the operating system, to fix a broken system that cannot boot normally, to manage hardware at the deepest level, to create and manage all other user accounts. Root is the account that makes all of that possible.
But root’s unlimited power is precisely what makes it dangerous for everyday use. A typo while operating as root can delete essential system files. A piece of malware running as root has immediate, unrestricted access to everything. An accidental rm -rf command targeted at the wrong path can wipe an entire system in seconds. These are not theoretical risks — they are the reason that Linux evolved strong conventions around minimizing root usage and are why modern distributions like Ubuntu disable direct root login entirely.
This article explains what the root account is technically, how it differs from regular users and from sudo, what it can and cannot do, when legitimate use of the root account is genuinely appropriate, how to use it safely on the rare occasions when you need it, and the best practices that protect your system from the risks that come with root’s unlimited power.
The Root Account: Technical Foundation
Root’s Identity
Every Linux user account has a unique numeric identifier called a User ID (UID). Regular user accounts receive UIDs starting from 1000 on most distributions. System service accounts use lower UIDs (typically 1–999). The root account always has UID 0 — and this specific number is what grants root its special status.
$ id root
uid=0(root) gid=0(root) groups=0(root)The Linux kernel does not recognize “root” as a special name — it recognizes UID 0 as a special identity. When a process runs with effective UID 0, the kernel grants it the elevated privileges associated with root. The account named “root” has UID 0, but technically any account with UID 0 would have the same privileges (though having multiple UID-0 accounts is a serious security misconfiguration to avoid).
Root’s Home Directory
Unlike regular users whose home directories live in /home/username, the root user’s home directory is /root — at the top level of the filesystem, separate from all regular user home directories. This placement reflects root’s special status and keeps root’s personal files separated from the regular user space.
$ ls /rootOn a freshly installed system, /root contains only basic shell configuration files. System administrators accumulate scripts, notes, and tools here over time.
Root’s Shell and Environment
Root uses Bash as its default shell on most distributions, just like regular users. However, root’s environment differs in several important ways:
The shell prompt displays # instead of $ at the end, universally indicating a root shell. This visual distinction exists so that users always know when they are operating with root privileges — the difference matters.
Root’s PATH variable typically differs from a regular user’s PATH. It includes additional directories like /sbin and /usr/sbin that contain system administration commands not usually needed by regular users.
Root’s shell configuration files are ~/.bash.rc and ~/.pro.file in /root/ — entirely separate from any regular user’s configuration.
What UID 0 Actually Unlocks
The Linux kernel grants processes running as UID 0 a set of capabilities that are denied to all other processes:
Bypassing file permission checks. A root process can read, write, and (with one important exception) execute any file regardless of the permission bits set on that file. The permission system, which controls all file access for regular users, is largely invisible to root.
The execute exception. Root cannot execute a file that has no execute bits set for anyone. A file with permissions ---------- cannot be executed even by root. This prevents root from accidentally running arbitrary data as a program — if a file has no execute permission for anyone, it is almost certainly not intended to be executed.
Binding to privileged network ports. Network ports below 1024 (called privileged ports) can only be bound by processes running as root. This is why web servers (port 80, port 443), SSH servers (port 22), and other standard services typically start as root before dropping to a less privileged account after binding their ports.
Managing all processes. Root can send signals to any process, change any process’s priority, and kill any process regardless of which user owns it.
Managing user accounts and groups. Only root can create new user accounts, delete accounts, change passwords for other users, and manage group memberships.
Modifying the system. Loading and unloading kernel modules, configuring network interfaces, mounting and unmounting filesystems, changing the system clock — these operations require root.
Accessing all files. Root can read any file, including private key files, password hashes, other users’ private documents, and encrypted configuration files (assuming the decryption keys are stored on the system).
Root vs. Regular Users: The Fundamental Difference
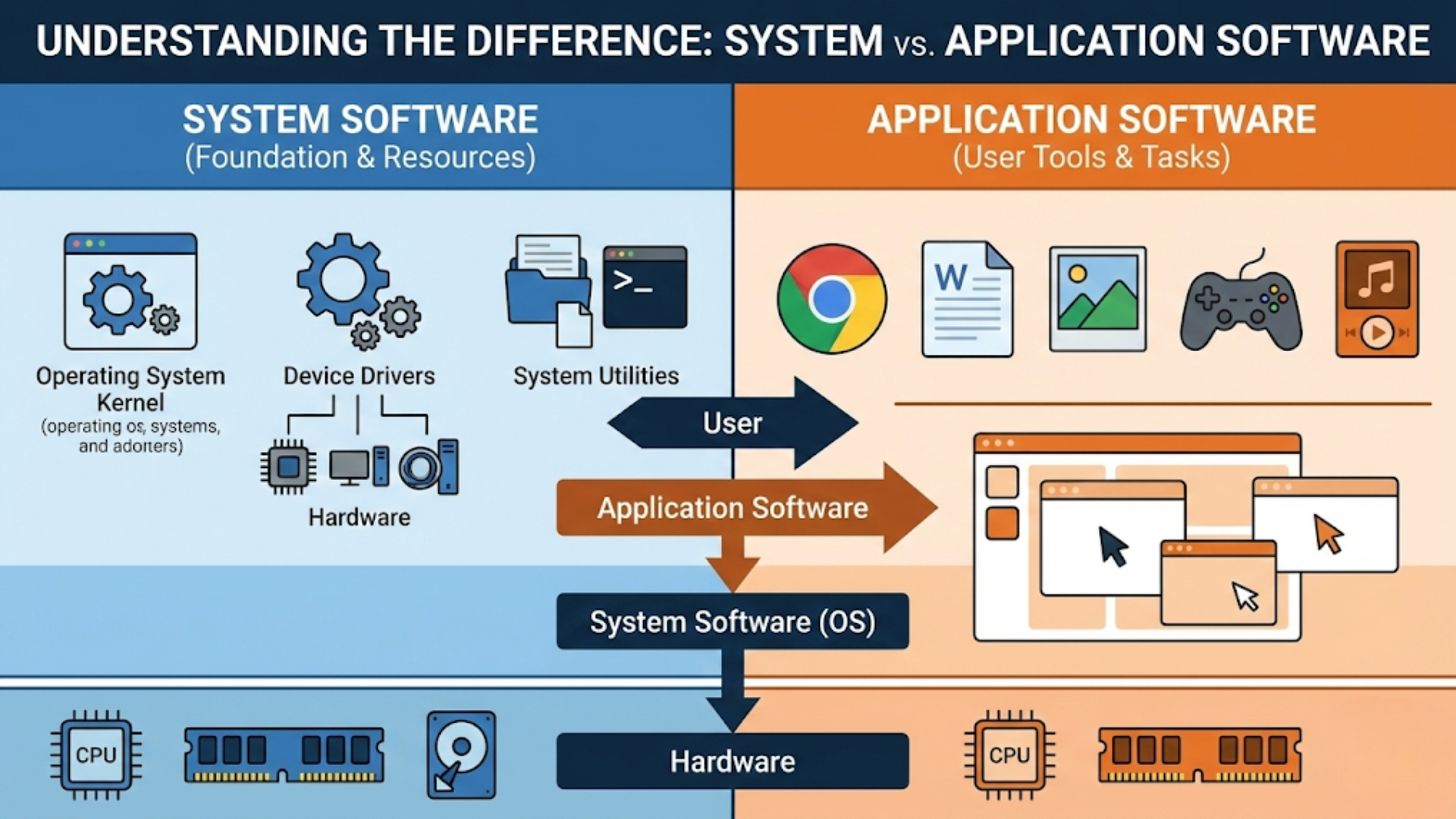
The contrast between root and a regular user account reveals the essential design philosophy of Linux’s security model.
What a Regular User Can Do
A regular user account is intentionally limited:
Reading and writing is restricted to files and directories the user owns or has been explicitly granted permission to access. A regular user cannot read /etc/.shadow (which contains password hashes), cannot read other users’ private files in /home, and cannot modify system files in /etc, /usr, or /var.
Running programs is permitted for any executable the user has execute permission for — including programs in /usr/bin (which are executable by all users). But a regular user cannot install new system-wide software, cannot modify system executables, and cannot run programs that require elevated privileges.
Process management is limited to the user’s own processes. A regular user cannot kill another user’s processes, cannot change their priority below a certain limit, and cannot adjust other users’ resource allocations.
Network administration is largely off-limits. Regular users cannot bind to privileged ports, cannot configure network interfaces, and cannot modify routing tables.
These limitations are not inconveniences — they are the design. By constraining what regular users can do, the system ensures that mistakes and security compromises in user-level software cannot damage the system or other users’ data.
What Root Can Do That Regular Users Cannot
Root’s capabilities represent everything outside those limits: modifying system files, managing all processes, accessing all data, controlling hardware directly, and administering all other user accounts. The complete list of root’s capabilities is effectively “everything the kernel allows.”
The Security Implication
The security value of this separation is clear: if a malicious program runs as a regular user and compromises that user account, the damage is limited to whatever that user had access to — their files, their processes, their data. The system itself, other users’ data, and administrative functions remain protected.
If that same malicious program runs as root — or if it exploits a vulnerability to escalate its privileges to root — the entire system is compromised. Every file, every account, every system function is accessible and modifiable. Recovery from a root-level compromise typically requires reinstalling the operating system and rotating all credentials.
This asymmetry is why the principle of least privilege — run with only the privileges you actually need — is so important, and why running as root for everyday tasks is strongly discouraged.
Root on Different Linux Distributions
Not all Linux distributions handle the root account the same way. Understanding these differences prevents confusion.
Ubuntu: Root Is Disabled by Default
On Ubuntu and most Ubuntu-based distributions (Linux Mint, Pop!_OS, etc.), the root account exists but is disabled for direct login. During Ubuntu’s installation, the root account is created with no password set — meaning you cannot log in as root by entering a password, because no password is accepted.
Instead, Ubuntu gives the initial user account sudo privileges, allowing that account to perform administrative tasks with sudo command while being protected by their own user password and the audit trail that sudo provides.
This design decision — made deliberately by Canonical — reflects the belief that most users should never need to log in directly as root. All legitimate administrative tasks can be performed through sudo. The security benefit is that even if an attacker discovers your user account password, they cannot directly log in as root — they would also need to compromise the sudo configuration.
To enable the root account on Ubuntu (not recommended for most users):
$ sudo passwd rootThis sets a root password, enabling direct root login. Use this only if you have a specific need and understand the security implications.
To disable it again:
$ sudo passwd -l rootFedora: Root Is a Normal Active Account
On Fedora and most Red Hat-based distributions (RHEL, CentOS Stream), the root account is fully active with a password set during installation. You can log in directly as root either at the console or through SSH (though SSH root login is typically disabled by default for security reasons).
Regular users on Fedora gain administrative access through the wheel group (the traditional Unix name for the administrative group), which grants sudo access. The convention is still to use sudo for administrative tasks rather than logging in as root.
Arch Linux: Root Must Be Configured Deliberately
On Arch Linux, which is installed manually rather than through a graphical installer, the root account is the only account initially. The installation process involves setting a root password, performing all initial configuration as root, and then creating a regular user account with sudo access as one of the final steps. This reflects Arch’s philosophy of explicit configuration over defaults.
sudo vs. Root: Understanding When Each Is Appropriate
A common confusion among new Linux users is the relationship between using sudo and actually logging in as root. They both involve elevated privileges, but they are quite different in practice.
sudo: Targeted, Temporary, Logged
sudo command runs a single specific command with root privileges. Before and after that command, you remain a regular user. The use is logged. You provide your own user password for authentication. If someone compromises your user account, they can use sudo — but only by knowing your password, and every sudo action is logged.
This is the appropriate tool for the vast majority of administrative tasks: installing packages, editing system configuration files, restarting services, managing users.
Root Shell: Sustained, Unlogged Actions, Higher Risk
When you open a root shell (via sudo -i, sudo su, or direct root login), you operate as root for the entire duration of that session. Every command runs with root privileges — no per-command authentication check, no per-command logging (only the initial shell creation is logged). You can make any change, delete any file, and run any program without further authorization prompts.
This is appropriate when you need to perform many administrative tasks in sequence — such as during initial system setup, disaster recovery, or complex system reconfiguration — but carries higher risk than targeted sudo use.
When Direct Root Login Makes Sense
There are legitimate scenarios where logging in directly as root (rather than using sudo) is appropriate or even necessary:
Single-user/recovery mode: When a system cannot boot normally, it boots into single-user or recovery mode as root. In this environment, you may not have a regular user account available, and the sudo infrastructure may not be operational. Root access is how you diagnose and fix the problem.
System installation: When installing a new Linux system, the installer often operates as root. Some minimal installation environments may not have sudo configured.
Emergency console access: If the filesystem is damaged, if user account databases are corrupted, or if critical system services are failing, direct root console access may be the only way to repair the system.
Highly automated server environments: Some server configurations run entirely as root — particularly container workloads where the container’s root is isolated from the host system. This is not a recommendation for general use, but it is a reality in specific technical contexts.
When You Should NOT Use Root
Understanding when NOT to use root is at least as important as understanding when you should. Most inappropriate root usage falls into recognizable patterns.
Everyday Computing Tasks
Browsing the web, writing documents, playing music, editing photos, programming in your home directory, managing your own files — none of these require root access. If you feel compelled to use root for everyday tasks, something is wrong with either your permissions setup or your habits.
Installing Software Through a Package Manager
sudo apt install package or sudo dnf install package handles package installation correctly with targeted elevated privileges. You should never log in as root to install software — sudo is exactly the right tool for this.
Editing Configuration Files
sudo nano /etc/.hosts or sudoedit /etc/.hosts handles privileged file editing correctly. A root shell just to edit one configuration file is unnecessary and adds risk.
Running Applications That “Need Root”
Some applications or tutorials suggest running programs as root to avoid permission problems. This is almost always the wrong solution. If an application cannot access a file or directory it needs, the correct fix is to adjust the file permissions or ownership — not to run the application as root. Running an application as root gives that application (and any vulnerabilities in it) unrestricted system access.
The common example is running a web browser as root to access a system configuration file. This is dangerous: browsers execute JavaScript and process untrusted web content. A compromised browser running as root is a system-level compromise.
Scripted or Automated Work
Scripts and automated processes should run with the minimum privileges needed. A backup script that needs to read certain files should run as a user with read access to those files — not as root. A monitoring script that checks disk space can run as any user. Reserving root for automation that genuinely requires it (modifying system configuration, starting system services) limits the blast radius of script errors.
How to Use the Root Account Safely
When you do need to work as root, these practices minimize risk.
Prefer sudo for Individual Commands
Even when you need to perform multiple administrative tasks, consider whether you can use sudo for each command individually rather than opening a root shell. The per-command structure makes the operations more deliberate and maintains the audit trail.
$ sudo systemctl stop nginx
$ sudo cp /etc/.nginx/nginx.conf /etc/.nginx/nginx.conf.backup
$ sudo nano /etc/.nginx/nginx.conf
$ sudo systemctl start nginx
$ sudo systemctl status nginxFive commands, each with explicit sudo, each logged. Equivalent to a root shell session but with better accounting.
When Using a Root Shell, Limit Its Scope
If you do open a root shell, limit how long it remains open. Complete the specific set of administrative tasks that required it, then exit immediately.
$ sudo -i
# [perform administrative tasks]
# exit
$Never leave a root shell open and unattended. If you need to step away from your computer during administrative work, lock the screen or close the root shell and reopen it when you return.
Double-Check Destructive Commands
Before executing any destructive command as root — particularly rm, mkfs (format a filesystem), dd (write directly to a device), or anything that modifies disk structure — verify the target explicitly. Run a dry-run or preview step first when the tool supports it.
# ALWAYS check before destructive operations
$ ls /path/to/files/you/plan/to/delete # Preview what will be deleted
$ rm -ri /path/to/files/you/plan/to/delete # Interactive deletion with confirmationAs root, there is no Trash — deleted files are gone immediately.
Avoid Root for File Creation in User Directories
Creating files as root in user home directories is a common mistake that causes frustrating permission problems. If you create /home/sarah/config.txt as root, the file is owned by root and sarah cannot edit it without sudo.
If you need to create files in a user’s home directory, either:
- Switch to that user first:
sudo -u sarah touch /home/sarah/config.txt - Create as root and immediately fix ownership:
sudo chown sarah:sarah /home/sarah/config.txt
Keep Root’s PATH Clean
When running as root, be aware that the PATH may include directories that contain user-installed scripts or tools that could be malicious. A common security attack involves placing a malicious ls or cd script in a directory early in a compromised user’s PATH, hoping it gets executed when that user escalates to root.
The sudo -i command loads root’s own environment and PATH, providing a cleaner and more predictable execution environment than sudo commands that inherit the calling user’s environment.
Review What Commands Do Before Running Them as Root
Before running any command as root — especially commands you found online — understand what the command does. The Linux manual (man command) and command --help are your first resources. For complex commands, search for explanations.
The question “what does this command do as root?” should always have a clear answer before you execute it.
The Root Account in System Administration
For those who manage Linux systems professionally or semi-professionally, the root account’s role extends beyond occasional fix-it usage.
Initial System Configuration
When setting up a new Linux server, root access is typically required for the initial configuration: setting the hostname, configuring networking, creating user accounts, installing the base software stack, configuring system services, and setting up security policies. This initial work is legitimately performed as root or through extensive sudo use.
After initial setup, a well-administered server should require root access rarely — ongoing administration through sudo is sufficient for most tasks.
Disaster Recovery
When a system is broken — a failed disk, a botched update that broke the bootloader, a misconfigured system service that prevents normal login — root access through recovery mode or a live USB environment is how you diagnose and repair it. In these scenarios, root is not a privilege to be used cautiously but a necessary tool for system restoration.
Understanding how to access a root console through recovery mode (from the GRUB boot menu, choose “Advanced options,” then “Recovery mode,” then “root shell”) is valuable knowledge for Linux system administrators.
Security Auditing
Certain security tasks require root access to be thorough: checking file permissions across the entire filesystem, reviewing all running processes and their privilege levels, examining system logs from all sources, and auditing all installed software. These tasks, when performed deliberately and with appropriate authorization, justify root access.
Kernel and Driver Management
Loading and unloading kernel modules (device drivers), configuring kernel parameters through /proc/sys, building and installing custom kernels — all of these require root access. Advanced hardware configuration and system tuning operate at the root level.
Monitoring and Auditing Root Usage
On any system where security matters, monitoring what has been done with root privileges is important.
The sudo Log
As covered in the sudo article, every sudo command is logged. On Ubuntu/Debian systems:
$ sudo grep sudo /var/.log/auth.log | tail -20This shows the 20 most recent sudo uses, including who used it, when, from which terminal, and what command was run.
Direct Root Login Log
On systems where direct root login is enabled, root login events are also logged in auth.log:
$ sudo grep "root" /var/.log/auth.log | grep -i "session opened"Watching for Unexpected Root Activity
On a multi-user system or a server, unexpected root activity is a security signal worth investigating. Signs of concern include:
- sudo usage at unusual hours from accounts that do not normally use sudo
- Root login attempts (especially failed ones) from unexpected IP addresses
- New SetUID files appearing on the system (check with
find / -perm -4000 -type f) - New entries in the sudoers file or new members in the sudo/wheel group
- Unexpected cron jobs running as root
Regular review of auth.log and the output of sudo find / -perm -4000 -newer /var/.log/dpkg.log -type f (files with SetUID set that are newer than the last package manager activity) helps catch unexpected changes.
Root User Quick Reference
| Concept | Detail |
|---|---|
| UID | Always 0 — kernel identifies root by UID, not by name |
| Home directory | /root (not /home/root) |
| Prompt indicator | # (vs $ for regular users) |
| Default shell | /bin/bash (same as most users) |
| Can bypass file permissions | Yes — almost all checks skipped |
| Can execute non-executable files | No — execute bit must be set for someone |
| Ubuntu default state | Disabled (no password set) |
| Fedora default state | Active with password set during install |
| Preferred access method | sudo command for single commands |
| Root shell method | sudo -i (preferred) or sudo su |
| Always logged | Direct login: auth.log; sudo: auth.log with full command |
| Groups | Member of root group (GID 0) |
Conclusion: Power Wielded Wisely
The root user is not something to fear, but it is something to respect. Its unlimited power is what makes Linux systems manageable — without root, an administrator could not install a broken system, repair a critical failure, or perform the deep system management that keeps infrastructure running. Root is a necessary part of the Linux design.
But necessity does not mean routine. The appropriate relationship with root for most Linux users is one of deliberate, infrequent use: reaching for it through sudo when a specific task requires it, completing that task efficiently and carefully, and returning to the limited but sufficient regular user environment for everything else.
The best Linux users and administrators are not those who operate as root most comfortably. They are those who understand precisely when root is needed and why, who reach for sudo with understanding rather than habit, and who keep root access as the rare and powerful tool it is designed to be — used deliberately, carefully, and always with awareness of what that power means.
Understanding root is not just technical knowledge. It is a component of the security mindset that makes the difference between a well-run Linux system and a vulnerable one.